Your Infrastructure, Your Rules.
Our cloud for your service.
Security tools that dictate architecture create friction. Forced cloud routing adds latency and compliance concerns. Hardware-only solutions don’t fit dynamic environments. Cloud-native options ignore existing on-premise investments.
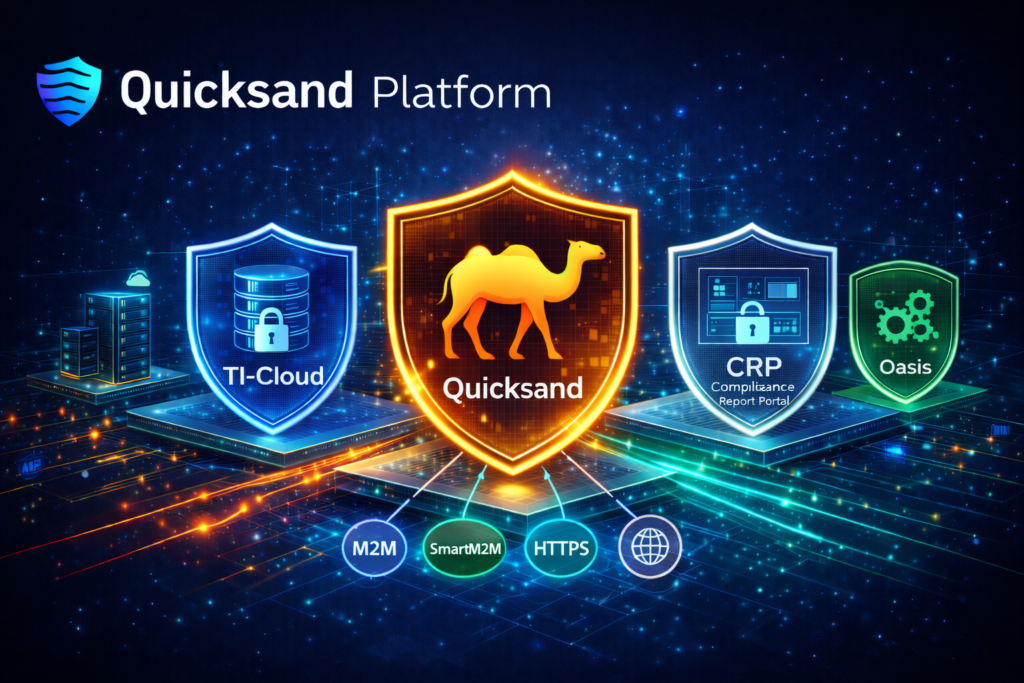
Quicksand adapts to your infrastructure reality—not the other way around.